Stale users
The presence of stale users within an app can pose several risks and challenges. These inactive or disengaged users may occupy valuable database space, impacting system efficiency and performance. Moreover, they can skew analytics and reporting metrics, making it difficult to assess user engagement and behavior accurately.
Stale user accounts can also become attractive targets for malicious actors seeking to exploit abandoned profiles for fraudulent activities or data breaches. To mitigate these risks, it's essential for app developers and administrators to regularly review and clean up inactive accounts, implement proper user lifecycle management practices, and encourage user engagement to maintain a healthy and secure user base.
How it works
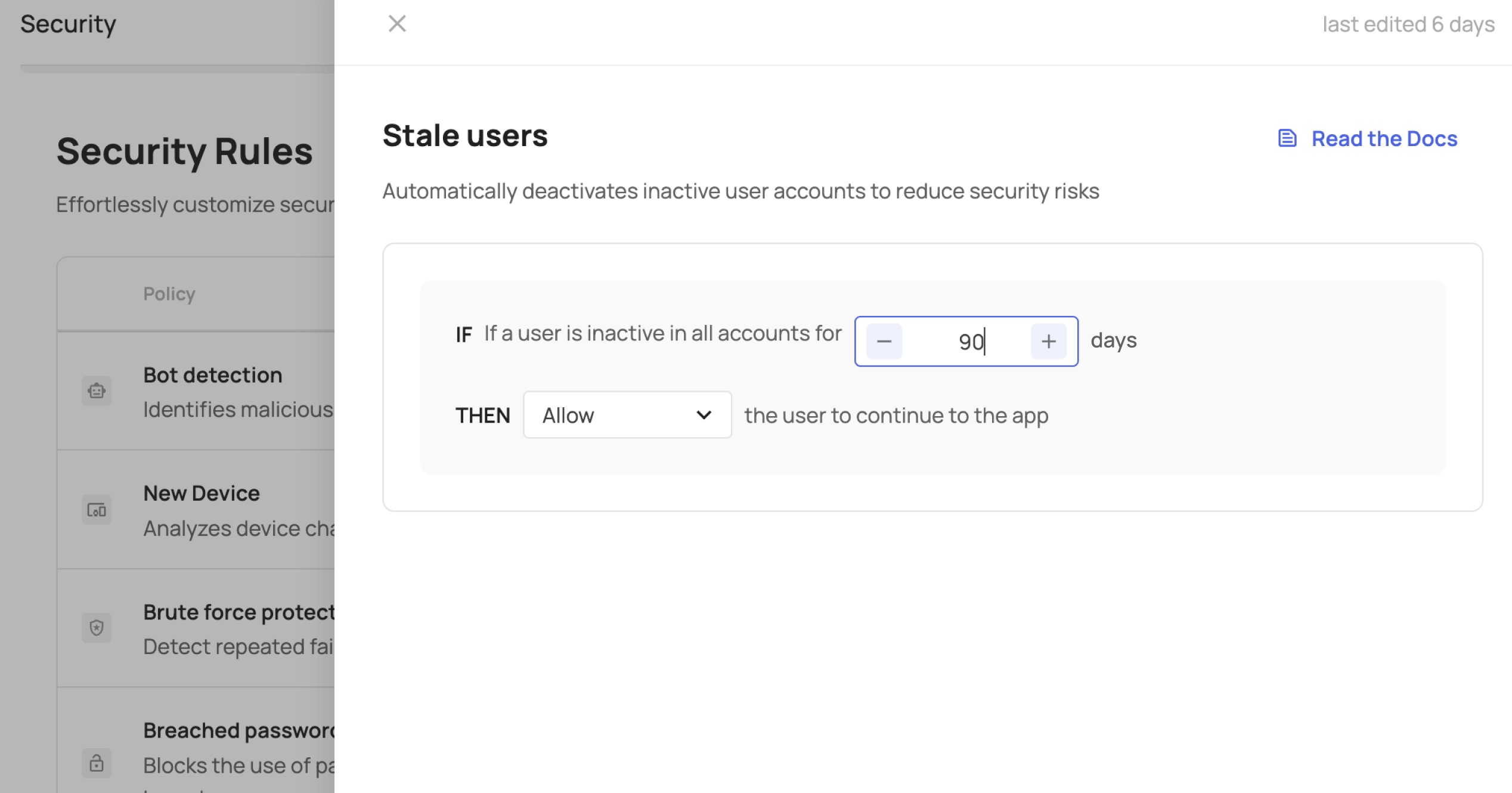
Once a day, we conduct a check on all your users to determine their last login to any of their accounts. If the number of days since their last login exceeds the configured threshold, the system triggers the identification of stale users for that specific user.
If you opt for Allow, Challenge, or Block, the selected action will take effect during their next login. However, if you choose Lock, the user will be immediately locked during the daily check.
Configuring Stale Users
In the Frontegg Portal
Choose from the following actions when a user becomes inactive:
- Allow: Permit the user to access the app on their next login.
- Challenge: Introduce Multi-Factor Authentication (MFA) to verify the user on their next login. If successful, grant access to the app.
- Block: Prevent subsequent login attempts.
- Lock: Immediately restrict the user during daily checks.
User Experience
- Allow: The user is permitted to proceed to the app, marking them as non-stale.
- Challenge: The user undergoes a Multi-Factor Authentication (MFA) challenge. Upon successful completion, they proceed to the app and are no longer considered stale. If unsuccessful, their login is blocked.
- Block: The user receives a failed login message.
- Lock: The user is notified that their account is locked.
Notifying End Users of Stale User Logins
You can choose to notify users when there is a login attempt once they are stale by checking the relevant checkbox.
Analyzing Stale Users in Your App
If you're curious about the frequency with which stale users login to your app, you can track their login occurrences over time, along with the locations where these logins occurred. Security Events.
Updated 3 months ago