Advanced SSO for Multi-tenancy
Prerequisites
For Frontegg Embedded Login users, ensure your SDK version is updated:
@frontegg/[email protected]
@frontegg/[email protected]
@frontegg/[email protected]
@frontegg/[email protected]
Frontegg's Advanced SSO for Multi-tenancy streamlines user access management across multiple applications under a unified single domain. This innovative feature enables organizations to establish multiple SSO connections within the same domain, effectively segregating data access according to team requirements. For instance, one team can configure an SSO connection to access a specific tenant's account exclusively, while another team can set up a different SSO connection for another account, ensuring that each team accesses only the data relevant to them. This approach enhances security by compartmentalizing access and simplifies the user experience by maintaining a single domain structure for multiple applications.
Frontegg requires domain validation for clients initiating an SSO connection via the admin portal as a default security measure to prevent domain abuse. This validation ensures that each domain is uniquely associated with a specific account and environment, reinforcing the security framework. In that case, a domain is validated and used per account and per environment. By enabling the SSO multi-tenancy feature, you allow your customers to use the same domain for several SSO configurations for their different tenants— thus allowing them to grant data access to specific users.
Configuring SSO for multi-tenancy
To configure SSO for multi-tenancy, go to Environments ➜ [NAME OF ENVIRONMENT] ➜ Authentication ➜ SSO ➜ Service provider ➜ Multitenancy SSO.
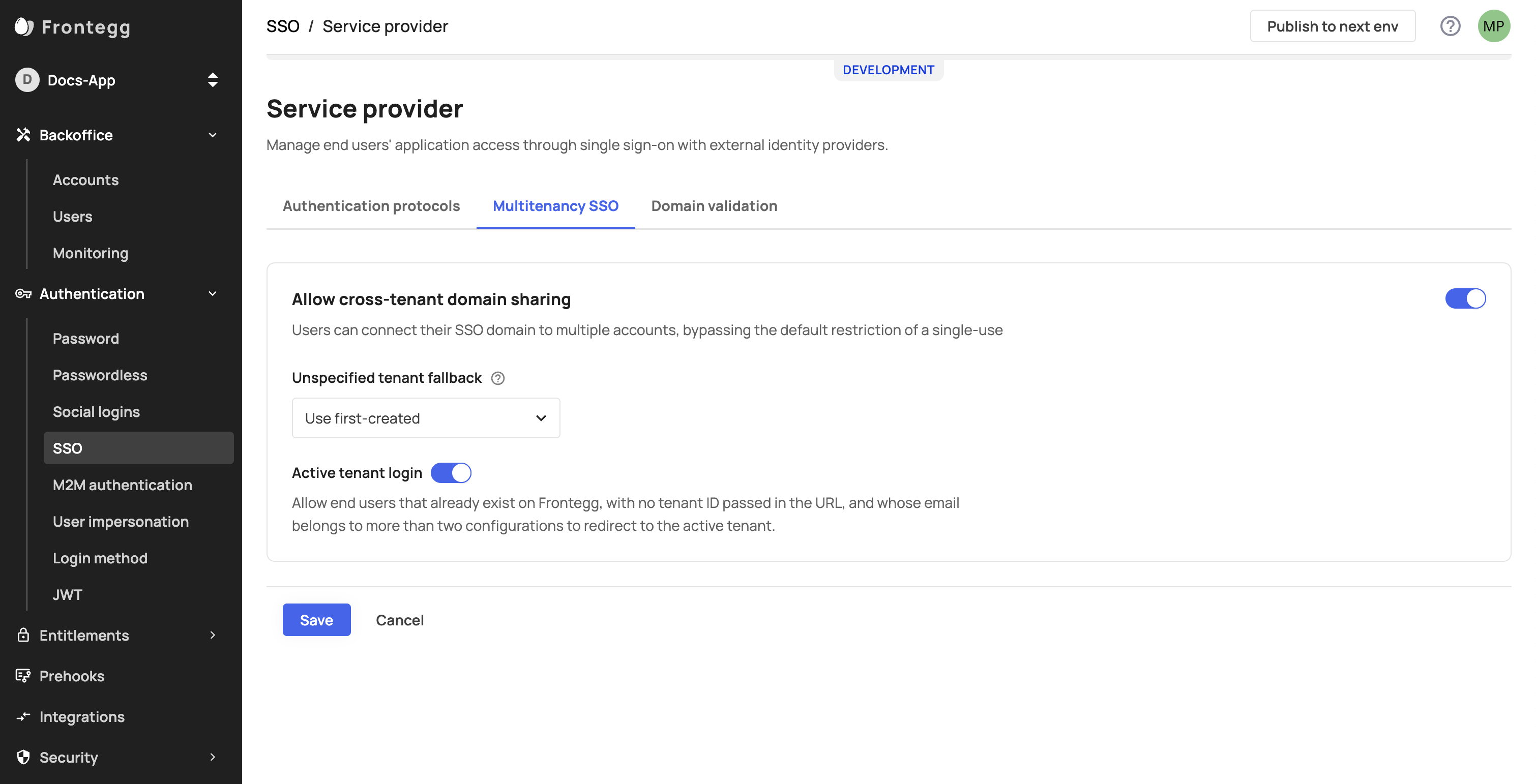
Allow cross tenant domain sharing
Allow cross tenant domain sharing Note that this field is optional and is set by default to
Use first-created. Since theactive tenant loginfield is bundled withUse first-created, it will be enabled automatically unless you explicitly disable it..Block the login - this field will block non existing user whose domain is associated to multiple accounts from proceeding with the SSO login, unless
tenantId={{tenantId}}will be passed in the search params of the login route. In this case, the user will be prompted to use the default authentication method (i.e., password / passwordless).Use first-created - this option will redirect a non-existing user whose email domain is used in several SSO connections (and isn't passing
tenantId={{tenantId}}in the login), to the tenant through which the first SSO configuration was created and is therefore linked to the user domain.Active tenant login - A configuration bundled with one of the following options:
Block the login / Use first-createdwhich redirects an existing user (whose email domain is used in more than one SSO configuration) to the user's currently active account.Note that if a non-existing user logs in via an IDP initiating an SSO flow, the user will be redirected to the relevant account and
allow cross tenant domain sharingwill have no impact on that user's flow.
Redirecting users with multiple SSO configurations
When a user domain is associated with multiple SSO configurations across multiple accounts, the user will need to pass their tenantId in the login URL so Frontegg can redirect them to the SSO endpoint associated with that account. If a user exists but does not pass their tenantId— Frontegg will default to the account redirect where the user's first SSO configuration was created.
The following example URLs contain the tenantId identifier
// Hosted login
https://[your-frontegg-workspace-url]/oauth/account/login?tenantId={{tenantId}}
// Embedded Login
https://[your-application-url]/account/login?tenantId={{tenantId}}
Updated 8 months ago